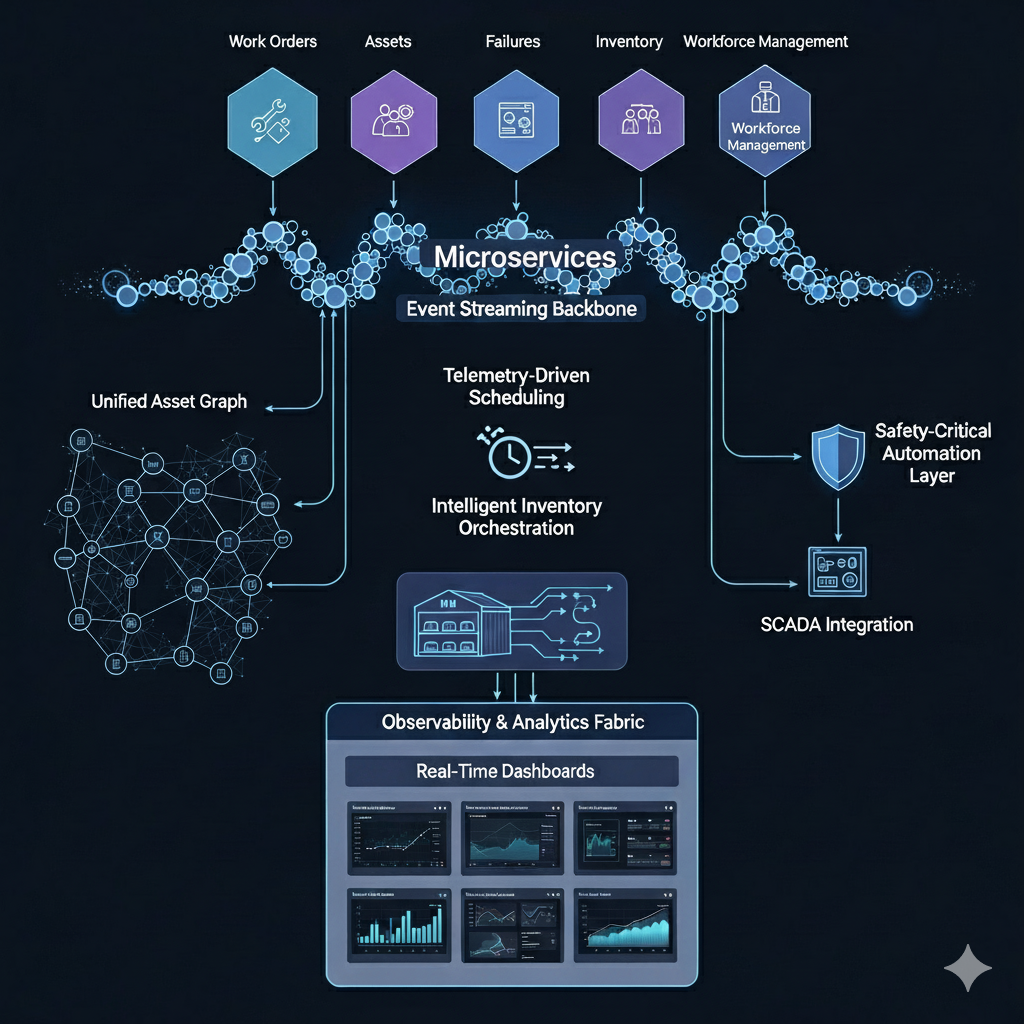
Operational Technology Visibility Platform
Operators managing large-scale power systems were struggling with fragmented tools that provided little to no visibility into their operational technology (OT) estate. Assets such as relays, remote terminal units (RTUs), routers, and industrial PCs came from multiple vendors and generations, often with inconsistent firmware and patch histories. This made it difficult to track vulnerabilities, ensure compliance with global standards, or respond proactively to cyber risks. As a result, operational overheads were high, compliance audits were painful, and systems were exposed to increased cyber and operational risk.
Solution
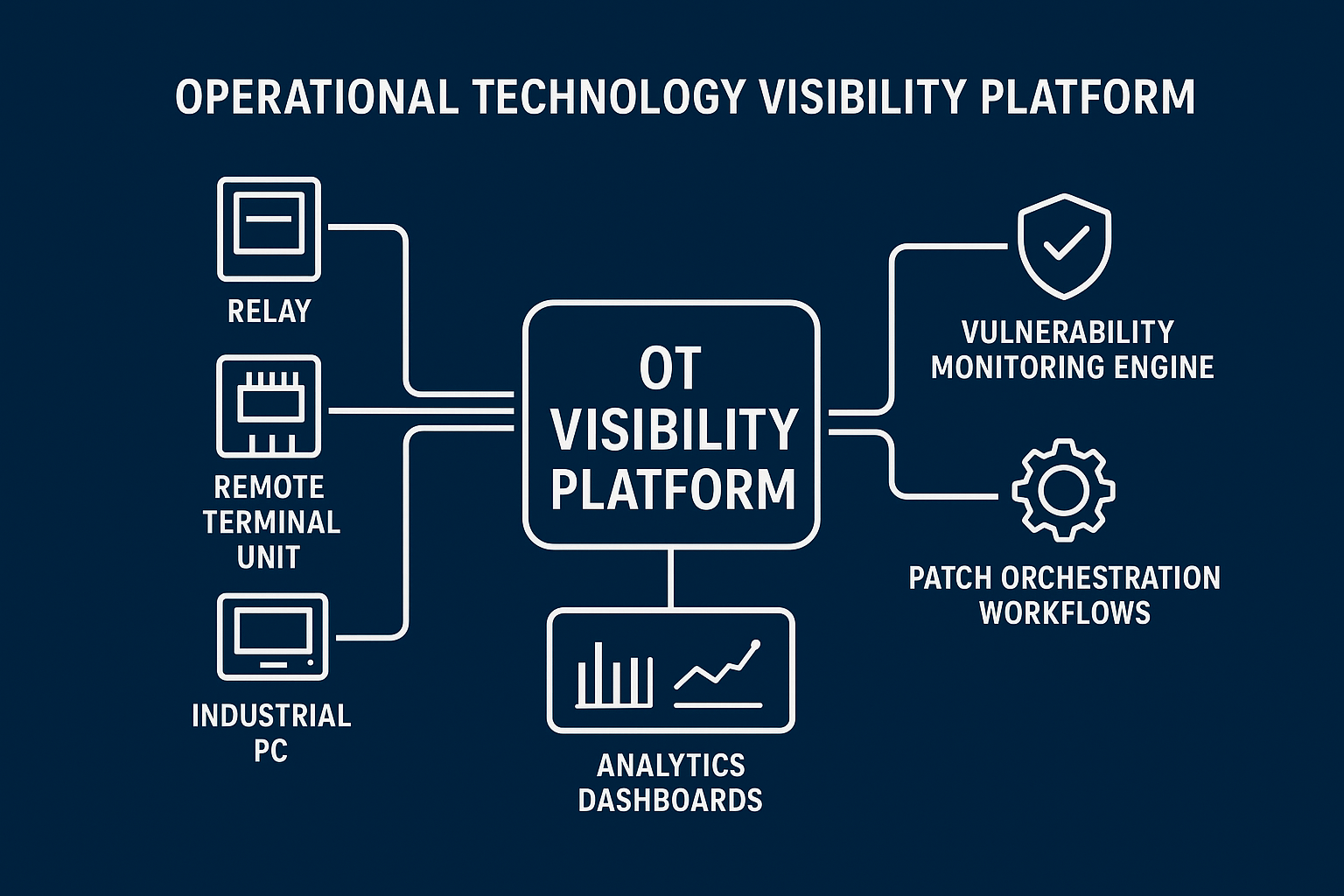
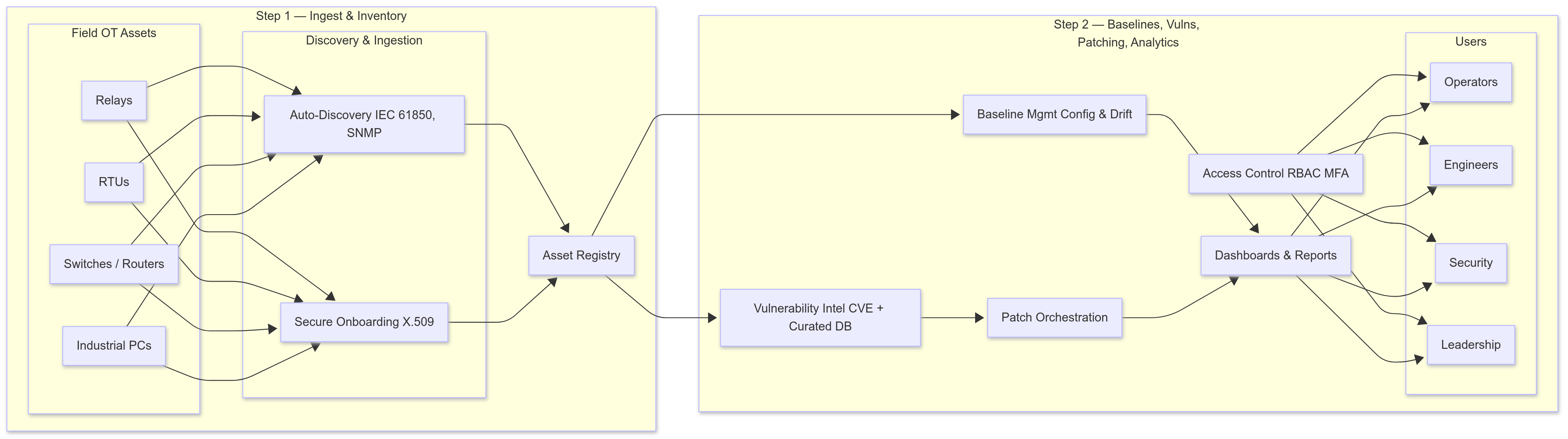
I led the design of an OT Visibility Platform that consolidated OT asset data, vulnerability intelligence, and patch workflows into a single, contextual platform. By integrating with vulnerability databases and industry protocols, the platform allowed operators to see a real-time inventory of their multi-vendor OT assets, track baseline configurations, and receive asset-specific vulnerability alerts. It also included patch orchestration workflows that enabled operators to plan, track, and document remediation steps in alignment with global standards such as IEC 62443, NIS-2, and NERC CIP. This provided operators with end-to-end visibility and control of their OT environment.
Impact
The platform shifted operators from reactive to proactive management of both security and compliance. Manual effort in patch tracking and reporting was significantly reduced, compliance costs were lowered, and cyber resilience was improved. Leadership gained actionable insights into the health, vulnerability posture, and compliance status of their OT estate. By providing a transparent and contextual view of OT operations, the platform allowed both operators and executives to make better-informed decisions on security and maintenance priorities.
Technical Highlights
- Centralized OT asset registry: Built to capture and contextualize multi-vendor, multi-generation components, including relays, RTUs, routers, and industrial PCs, with firmware and network configurations.
- Baseline configuration management: Defined software/firmware baselines and continuously monitored deviations to flag drift and configuration risks.
- Vulnerability monitoring engine: Integrated with curated vulnerability database to provide real-time, asset-specific alerts.
- Patch orchestration workflows: Enabled planning, tracking, and documenting of patch deployments with linked risk assessments and SLA compliance checks.
- Automated monitoring: Leveraged standard protocols (IEC 61850, SNMP) to track asset health, availability, and compliance continuously.
- Security-first architecture: Included role-based access control, MFA, and certificate-based device onboarding for secure data in motion and at rest.
- Analytics dashboards: Delivered transparency into OT asset health, vulnerability posture, and patching progress, enabling contextual decision-making for both operators and executives.